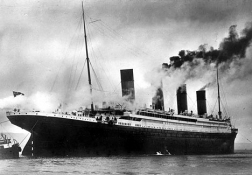
 One hundred years ago this weekend, the RMS Titanic hit an iceberg off the coast of Newfoundland and sank. The event was big news then and has remained so for a century, due in no small part to the number of wealthy people who died or were aboard: John Jacob Astor IV; Lucy, Lady Duff-Gordon; Molly Brown; Benjamin Guggenheim; and Isidor Straus. It was a bit as if the Kodak Theatre caught fire during the Academy Awards. (Compare the Titanic to the RMS Empress of Ireland, which sank in the mouth of the St. Lawrence two years later with a loss of more passengers, although considerably fewer crew. Celine Dion sings no songs about the Empress of Ireland.)
One hundred years ago this weekend, the RMS Titanic hit an iceberg off the coast of Newfoundland and sank. The event was big news then and has remained so for a century, due in no small part to the number of wealthy people who died or were aboard: John Jacob Astor IV; Lucy, Lady Duff-Gordon; Molly Brown; Benjamin Guggenheim; and Isidor Straus. It was a bit as if the Kodak Theatre caught fire during the Academy Awards. (Compare the Titanic to the RMS Empress of Ireland, which sank in the mouth of the St. Lawrence two years later with a loss of more passengers, although considerably fewer crew. Celine Dion sings no songs about the Empress of Ireland.)
There are many fascinating aspects of the story, including the recently uncovered evidence of what exactly caused the ship to sink — not a massive gash in its hull, as had long been supposed, but rather a buckling of the plates over five compartments, due in part to the failure of potentially substandard rivets. For want of a rivet, the Titanic was lost. And there’s also the interesting question of why there was so little panic among the passengers as the ship went down. But I want to focus on one that I’m fairly sure is not going to get covered this week: the connection between the sinking of the Titanic and our modern Electronic Communications Privacy Act, the federal law that makes it a crime to intercept communications without either a court order or the consent of one of the parties.
The connection stems from the role of “wireless telegraphy” — radio, as it’s now known — in the Titanic disaster. Earlier on the day of the disaster, the Titanic had received no less than 6 messages over the wireless warning of ice, but only three of those made it to the bridge. The final warning, at 10:30pm local time, from the SS Californian, stated that the Californian was stopped for the night, stuck in an ice field nearby; but the Titanic‘s radio operator cut off the message with his reply: “Shut up! Shut up! I’m working Cape Race!”, meaning that he was attempting to communicate with the wireless telegraph station at Cape Race, Newfoundland, and the Californian‘s transmissions were interfering. At 11:30pm, the Californian‘s sole wireless operator turned off the set and went to bed. At 11:40pm, Titanic struck its iceberg, and at 12:05am, began transmitting distress calls — at first CQD, but later a newer distress call coming into vogue: SOS. The Californian, its wireless set turned off, received none of those. Instead, the captain of the Californian repeatedly tried to signal the passenger liner it had seen to the south by lamp, but there was no reply.
This failure to communicate seems scandalous, and it was seen that way at the time, but it is partly explained by the novelty of radio in 1912. The wireless operators on the Titanic were not part of the ship’s crew; they were employees of the Marconi Wireless Telegraph Company, and their primary job was to convey private messages to and from the ship’s passengers. They passed on the iceberg warnings to the bridge as a favor, but obviously the Titanic‘s operators did not view such ship-related tasks as their core mission. Similarly, the Californian‘s wireless operation was hardly viewed as an essential ship function; that explains why the radio went unattended after 11:30.
That would all change in the wake of the Titanic disaster, and finally we come to our connection to the Electronic Communications Privacy Act. Within a week of the sinking, a U.S. Senate subcommittee began an investigation. Among the problems cited was the failure to use wireless telegraphs effectively. The result was the Radio Act of 1912. The 1912 Radio Act required radio operators to be licensed, and set up a detailed set of regulations, mostly pertaining to distress calls. (It even specified the distress call to be used: “. . . – – – . . .”) But it also contained a provision prohibiting radio operators from “divulg[ing] or publish[ing] the contents of any messages transmitted or received by such station, except to the person or persons to whom the same may be directed, or their authorized agent, or to another station employed to forward such message to its destination, unless legally required so to do by the court of competent jurisdiction or other competent authority.” This was the first federal electronic communications privacy statute passed in the United States. (Several states had already passed laws protecting ordinary landline telegraph messages.)
But events were already overtaking Congress’s attempt to regulate in this area. In 1912 the technological breakthrough that would allow radio to become a mass media force was just emerging: the triode vacuum tube, which made it possible to amplify a radio signal in a receiving set so that the listener could hear voices and sounds, and not simply interruption of the signal. In other words, the triode made the devices that we now call “radios” practical. By the 1920s, the first broadcasts of sounds over the air were being made to receiving sets owned by members of the public. In order to account for the exploding popularity of radio, Congress passed the Radio Act of 1927, regulating the new industry.
In the course of doing so, Congress updated, but did not fundamentally alter, the privacy provision for the wireless telegraphs that were still being sent, again requiring radio operators to preserve the secrecy of telegrams. But it also, essentially for the first time, inserted a general prohibition against the interception of private communications: “[N]o person not being authorized by the sender shall intercept any message and divulge or publish the contents, substance, purport, effect, or meaning of such intercepted message to any person….” “Intercept” was not defined, but it is often used as a term for someone other than the intended recipient obtaining a radio communication as it is being transmitted. Interception of a radio telegram means to acquire a signal — i.e., tune into the frequency on which it is being transmitted using some sort of receiver — and then obtain the contents by listening to it and decoding it. Section 605 of the Communications Act of 1934, passed seven years later, generalized the interception prohibition to “any interstate or foreign communication by wire or radio.”
The 1934 Act began a pattern that has troubled regulation of electronic communications privacy ever since: the re-use of old statutory language in new contexts. “Intercept” was clear enough for radio transmissions, but what does it mean to intercept a telephone call? Is it intercepted when someone overhears one side of the conversation, or listens in on an extension telephone, or attaches a recorder to the line with one party’s consent? The courts struggled with questions like those for three decades, until the modern Wiretap Act was adopted in 1968. The Wiretap Act defined “intercept” as “the aural acquisition of the contents of any wire or oral communication through the use of any electronic, mechanical, or other device.” 18 U.S.C. § 2510(4). So “acquisition” is officially in the definition now, but instead of defining the means of getting access to the communication — acquiring a signal — “acquisition” refers to the act of listening after access (“aural” means relating to the ear or sense of hearing). The only limitation on access in the definition is that it involve some sort of device.
So what about listening to a lawfully made recording of a conversation without the consent of a party? Is that an interception? Courts have held that it is not, on the theory that it would create far too many practical problems in enforcing the Act — it would be difficult to know in advance if listening to a recording was legal or not, and it would create innumerable potential violations arising from a single recording. Courts therefore distinguish such “aural acquisitions” by listening to a recording from others that do fall within the definition. But in order to do that, courts had to read in a requirement that the interception be “contemporaneous” with transmission. This has become particularly problematic after yet another amendment that largely left the statutory language in place — the Electronic Communications Privacy Act, passed in 1986. The ECPA broadened the Wiretap Act so that it included email, but only through minimal rewording of the existing Wiretap Act. In particular, the definition of “intercept” was altered to refer to “aural or other acquisition of the contents of any wire, electronic, or oral communication” through the use of a device. It’s not clear how the “contemporaneousness” requirement, introduced to exempt listening to recordings, fits with the typical way in which email communications are surveilled. The easiest way to monitor someone’s email is to make a copy of it as it sits in some intermediate, temporary storage somewhere on a computer network. Does it “acquire” an email to make a copy of it as it sits in memory on a router or other device en route to the recipient? Some courts have said no, others yes.
Congress has been toying with amending the ECPA for at least a year. One thing it could do to make the statute clearer is finally lay the ghosts of the Titanic to rest, and make the language fit for technology in 2012 rather than 1912.

It’s nice to see the Titanic mentioned here. Indeed, it struck an iceberg at 11:40 p.m. on April 14, 1912 and sunk at 2:20 a.m. on April, 15th. By coincidence, Abe Lincoln was shot on April 14th and died on April 15th. The Titanic disaster is fascinating for many reasons. One is that it took 2:40 minutes to sink, thus allowing for a thousand mini-dramas to play out and be retold by the survivors. The Empress of Ireland, on the other hand, sunk in 15 minutes. It was an older ship, half the size of the Titanic and did not have famous Americans on board.
As for the ECPA, I have no opinion but it was outdated regulations and vanity that caused the Titanic to only have 20 lifeboats. That was enough for barely half the people on board, had they been fully loaded. One of Titanic’s builders had wanted 48 lifeboats, and the ships davits could have held 48, but he was overruled on the grounds of aesthetics and deck space. Ironically, a possible over-reaction to the Titanic disaster caused more people to die in Chicago three years later, right on the river downtown.
I call it an over-reaction, because lifeboats for all means nothing when a ship lists too much. That happened this year with the Italian cruise ship, Costa Concordia. It listed so badly that only half the lifeboats could be lowered. Titanic was the rare large sinking ship that did not list so much that lifeboats could not be lowered.
In the S.S. Eastland disaster, 800 people died in 30 feet of water on the Chicago River. The ship capsized while being loaded with passengers for a day trip to Indiana. In reaction to the Titanic disaster, new rules required lifeboats for all. This made the Eastland top-heavy and when those boarding massed on one side of the ship to greet the new arrivals, she tipped over trapping and killing 800 souls.
The lesson to be learned is that imposing new regulations on systems not designed for such regulations can lead to unintended consequences.